An organization is required to make the necessary security arrangements to protect personal data in its possession or under its control as stated in The Protection Obligation of the Personal Data Protection Act in Singapore. You as an event organizer have to give your attendees a peace of mind when they submit their personal data to you. How should you go about keeping the personal data in your control secure?
Things to Consider for Security Arrangements
There is no single solution for event planners to comply with the Protection Obligation. You should consider adopting security
arrangements that prevent:
- Unauthorized access
- Collection
- Use
- Disclosure
- Copying
- Modification
- Disposal
- Similar risks
Other factors to consider are the nature of the personal data, the form in which the personal data will be collected (e.g. physical or electronic) and the possible impact on the attendee concerned if an unauthorized person obtains, modifies or disposes of the personal data.
Your event organization should:
- design and organize security arrangements that fit the nature of the personal data held by your organization and the possible harm that might result from a security breach
- identify reliable and well-trained personnel responsible for ensuring information security
- implement policies and procedures for appropriate levels of security for personal data of varying levels of sensitivity
- be able to respond to information security breaches promptly and effectively — should they happen
In addition, you could undertake a risk assessment exercise to determine whether your information security arrangements are good enough. The following factors may be considered when doing so:
- the size of your organization and the amount and type of personal data it holds
- who within the organization has access to the personal data
- whether the personal data is or will be held or used by a third party on behalf of the organization
Examples of Security Arrangements
Security arrangements can come in different forms, be it:
- administrative measures
- physical measures
- technical measures
- a combination of the above measures
Here are some examples of security measures you can consider implementing in your event organization:
1. Administrative measures
- Ensure that all staff are bound by confidentiality obligations in their employment agreements
- Implement policies and procedures (with disciplinary consequences for breaches) regarding confidentiality obligations
- Conduct regular training sessions for staff to impart good practices in handling personal data and strengthen the awareness of threats to the security of personal data
- Ensure that only an appropriate amount of personal data is held, as holding excessive data requires more effort in protecting
2. Physical measures
- Mark confidential documents clearly
- Store confidential documents in locked file cabinet systems
- Restrict staff access to confidential documents
- Use privacy filters to minimize unauthorized personnel from viewing personal data on laptops
- Dispose of confidential documents that are no longer needed through shredding or similar means
- Implement an intended mode of delivery or transmission of personal data that possesses the appropriate level of security
- Provide a summary of the personal data contained in storage so that personal data is accessed only when necessary
- Confirm that the intended recipient of personal data is the correct recipient to avoid undue disclosure of personal data
3. Technical measures
- Ensure your computer networks are secure
- Adopt appropriate access controls such as stronger authentication measures where appropriate
- Encrypt personal data to prevent unauthorized access
- Activate self-locking mechanisms for computer screens that are left unattended for a certain period of time
- Install appropriate computer security software and use suitable computer security settings
- Dispose of personal data in IT devices that are to be recycled, sold or disposed
- Use the right level of email security settings when sending and/or receiving highly confidential emails
- Update computer security and IT equipment regularly
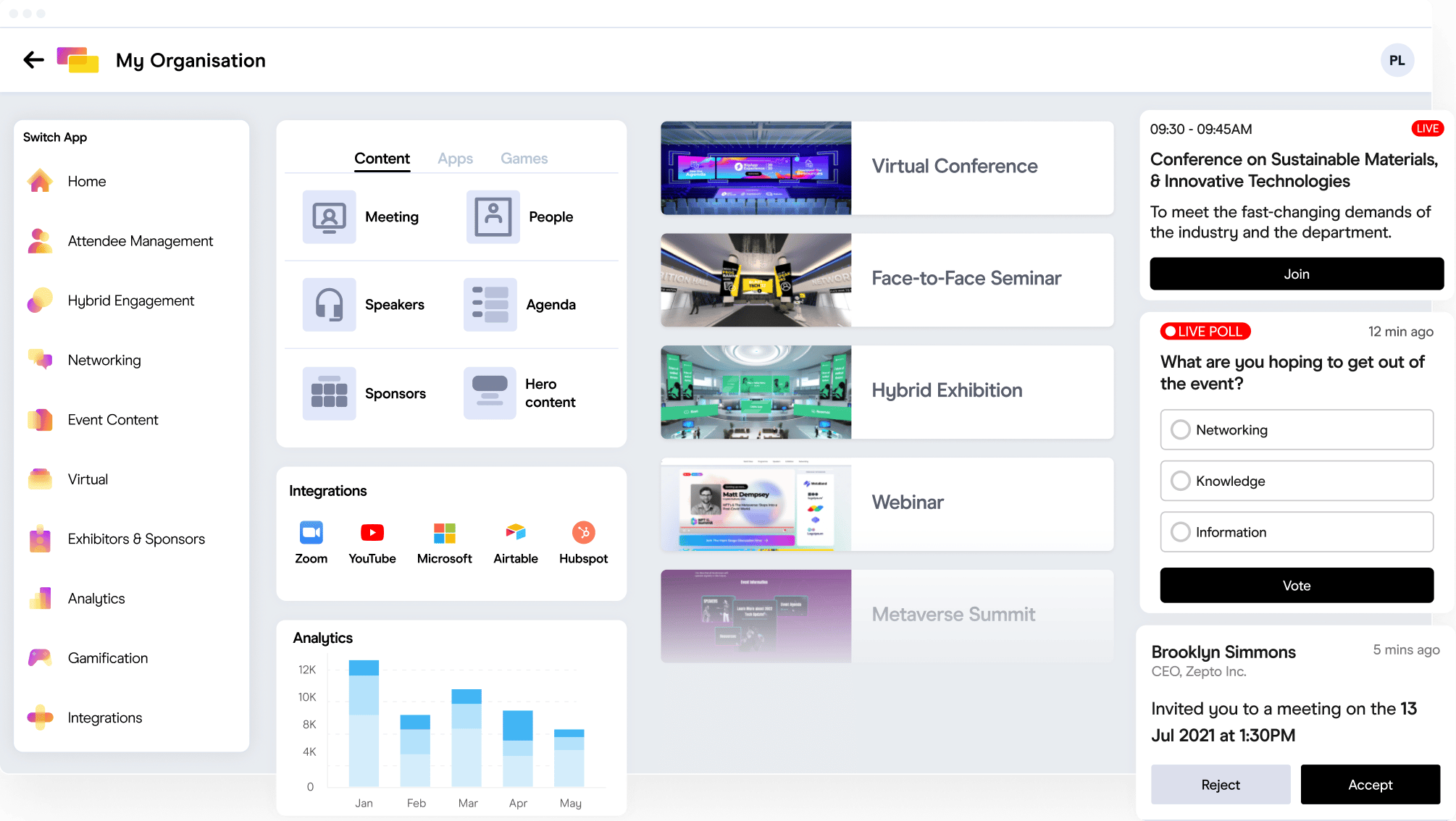
- Ensure that your attendee database is protected by an event management software that is PDPA-compliant
Now that you know how to ensure the security of personal data in your possession to comply with the PDPA in Singapore, review the security practices in your company and ensure your event organization is PDPA-compliant.
Get started with secure event management in Singapore.