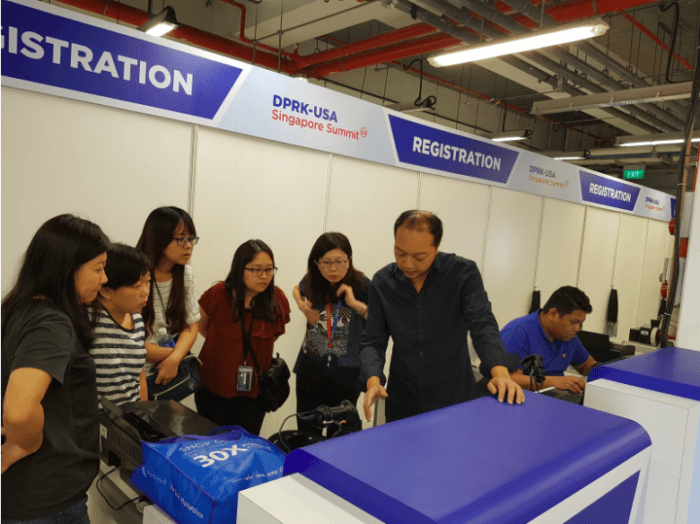
One of the most anticipated political meetings of 2018, the U.S.–North Korea summit, has finally occurred! GlobalSign.in was honored to be the official technical partner of this historic meeting, and Gevme was used as the event technology to power summit registrations on the ground.
In terms of preparation and planning, the focal point of this official meeting was security. Sentosa, the island where the summit took place, had been heavily policed for the previous five days. A great deal of focus was placed on ensuring foolproof event data protection. This required the development of a strong cybersecurity strategy, 24/7 surveillance of the servers, and extensive staff training.

When organizing official meetings like the Trump–Kim summit, it’s critical to understand that any little mistake can have profound consequences. Based on the experience we gained powering registrations at this iconic meeting, we’d like to share our top eight tips that will help you build a 100% secure event data environment.
Planning a government event
Being a tech partner at international governmental meetings means you need to have every infinitesimal process thoroughly planned. The design of your data protection strategy will depend on the information systems you use as well as the resources you can invest into security maintenance. Here are some basic tips on how to make your information infrastructure work as planned:
Level up the standards of data security significantly
Simply meeting minimum security standards doesn’t work when it comes to government event planning. Unless you’re convinced that the regulations you follow enable top protection of the most sophisticated event ecosystem, you’ll have to enhance them. Check out the major steps to upgrading data security standards before an important event:
- Conduct a gap analysis and identify your key data protection priorities, weak system management mechanisms, etc.
- Address compliance management, and upgrade due diligence requirements in case there are any third-party services you have to integrate with.
- Review recovery planning policies, and add the related scenarios you might need to address at a government event.
- Update recovery time objectives. It should take the minimum amount of time to address any ongoing issue.
- Analyse your current risk management strategy, taking into account all internal and external threats, such as APTs, connection breakage, etc. Complement your strategy with extra countermeasures, if needed.
- Polish your existing governance mechanisms. It’s important to ensure that all of the processes your team will have to accomplish within an event are aligned with strong risk-based governance principles.
Provide confidentiality instructions to the whole team
The second fundamental aspect of organising government events is ensuring confidentiality. Before you provide the event team with any logon data or access to sensitive information, non-disclosure agreements have to be signed. These legal contracts will help you regulate the following aspects:
- Identification of the parties involved
- Sharing of event-related information with any third parties
- Revealing of technologies used at the event to external organisations or individuals
Test a venue before an event

The venue you choose for a government event should complement your mission and comply with the key security needs. Start from the most basic requirement, which is the size of the venue. Events like the U.S.–North Korea summit attract immense media attention, so you have to ensure that the chosen venue can accommodate the expected number of reporters.
Next, check connectivity capabilities and the key restrictions. Find out whether it’s possible to set up a back-up connectivity system your team can rely upon in case any breakages occur.
Lastly, consider whether the venue can be declared a secure zone. For the Trump–Kim event, the area of Sentosa’s Capella Hotel was declared to be a “special event zone”, which implied the application of specific rules, like a ban on drones, aerosol paint, explosives, and flares across the area. If security measures mean a lot at your event as well, clarify these issues with a venue host.
Find software and online services support
The first step to building a secure information infrastructure is finding a reliable SIEM system. As an event tech provider, it’s important to ensure that the SIEM system you offer your client is compliant with the cybersecurity policy your client wants to follow. Specifically, a strong SIEM system should cover effective log management, scalability, deployment, and more. Before engaging in the organisation of a government event, update your software and major services to match your client’s strategy. Also, plan system maintenance in advance to prevent possible threats. During the North Korea–U.S. summit, our team facilitated 24-hour server surveillance to be able to identify and deter any attacks.
Test software, hardware, and onsite layouts before the event
Pre-event testing is the holy grail. As has been said before, every tiny detail can make a huge impact on overall performance. Obviously, you don’t want to fail because of a breakage that could have been easily fixed before an event. To avoid this, you will have to conduct extensive system testing. In terms of software performance, you can verify it through the use of scalability, endurance, load, stress, and spike tests. Concerning hardware diagnostics, there’s a huge list of testing activities you should exercise, from CPU and register tests to transient error monitoring. Lastly, ensure that onsite layouts work by testing every device separately and then in combinations (laptop–printer, tablet–printer, etc.) To minimize risks, appoint people who will be responsible for different types of system testing and maintenance, both before and during the event.
Give clear instructions to the onsite team at the event
Even with the best technology at your fingertips, you won’t be able to move the needle without a well-trained team. Organise an extensive staff training in which you’ll provide clear instructions on aspects such as cybersecurity threats prevention, system maintenance, risk-based governance, and more. Develop scenarios for different types of situations, and ensure that your staff is trained to take the right measures in each of these scenarios.
Conclusion
Powering events that make headlines around the world is a challenging task, but let’s be honest—the feeling of being a part of something as big as the North Korea–U.S. summit is worth a couple of sleepless nights. We hope that these eight tips on how to be a tech partner at government events will help you reach new heights with minimum stress.