Most event organizers will want to ensure there are as many attendees booked in for their conferences and workshops as possible, but not if it means having to accommodate uninvited visitors.
This issue was highlighted in Britain at the recent Conservative party conference, when Defence Minister Philip Hammond was heckled by two retired soldiers over cuts to army budgets. Indeed, writer Quentin Letts said in a review of the event that there were several “gatecrashers” and”attention-seeking individuals” who managed to get in front of cameras during the four days in Manchester.
Although they were escorted from the premises by security – and most event organizers will not experience putting together anything as high-profile as a party political conference – it does raise the question of how to ensure gatherings do not turn into a free-for-all.
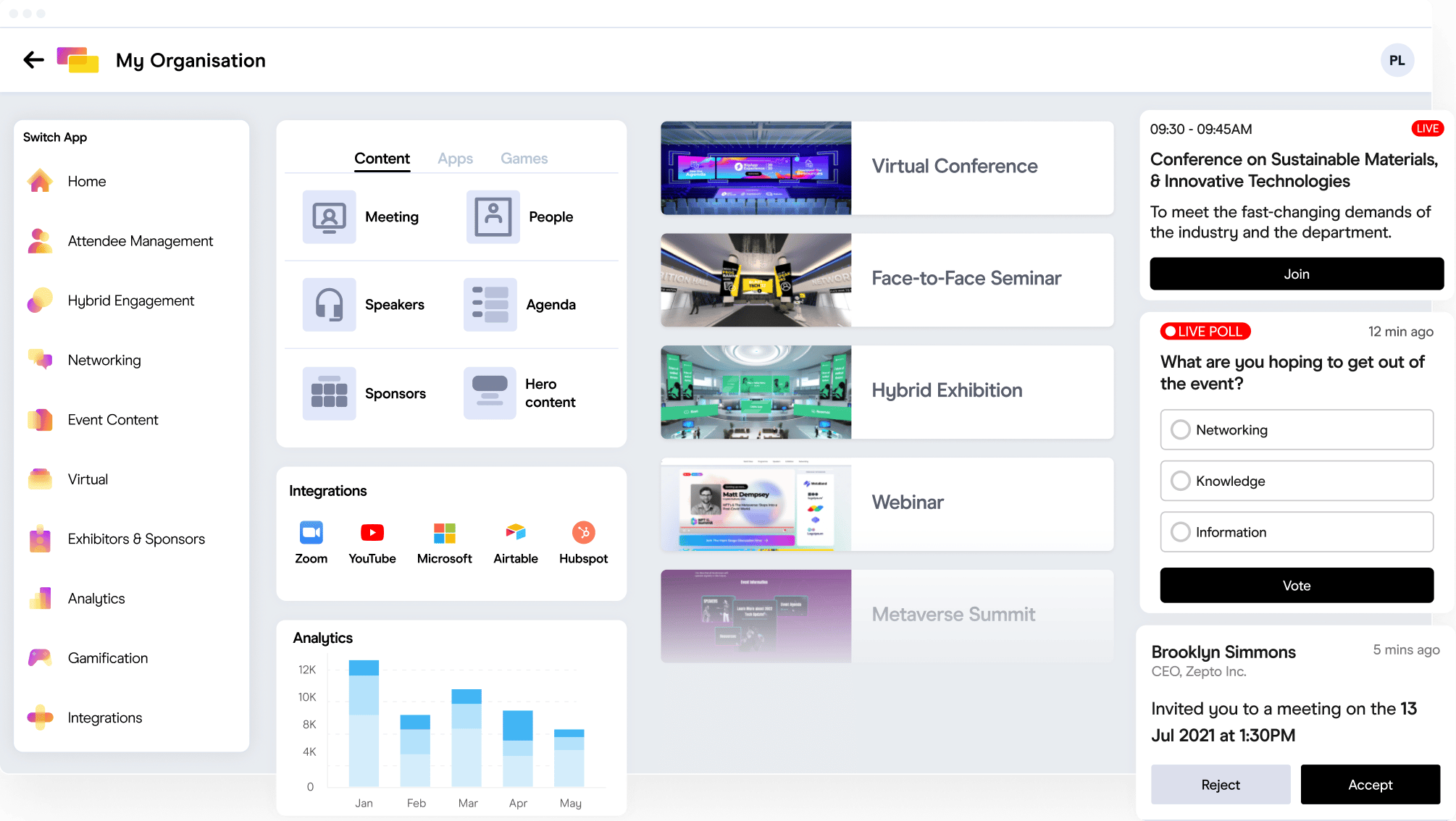
Fortunately, there are several measures that can be put in place to prevent this, starting with using an Event Data Management software to personalize everything at the registration process.
1. Start building your unwanted guest list
The unwanted guest list for most companies would include their competitors or unknown guests using freemail accounts. You can easily start building this list for a start using known email domains. Save this as a Smart List for subsequent usage during campaign execution.

Build your own List of unwanted guest by filtering based on email domain

Save this as a Smart List for auto-updates in event if any contact in your database meets this criteria
2. Exclude your unwanted guests from your e-communications
Leveraging on the unwanted guest list that you have built in Step 1, exclude this unwanted guest list from your email communications, so as to ensure that they are not made aware of the event you are holding, especially if this is a private event.

Exclude your unwanted guests from your email communications
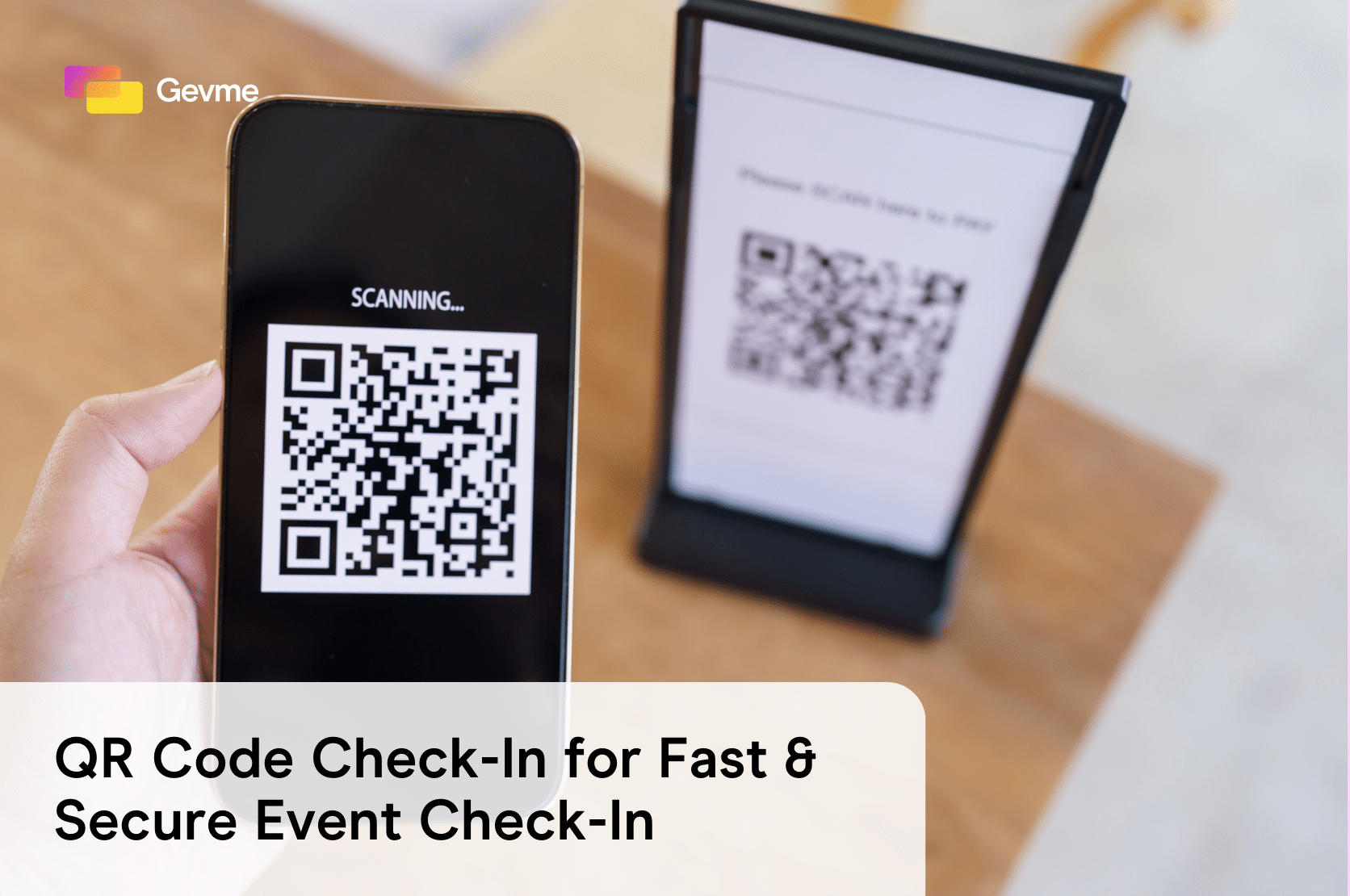
3. Send personalised confirmation with unique Bar Code/ QR Code
Send personalised e-ticket confirmation with a unique Bar Code and/or QR Code to identify the user. You can subsequently verify the users via an on-site mobile check-in app when scanning the QR Code. Have the name printed on the ticket so that you can do a quick verification via photo id when needed.

Use an e-ticket with a unique bar code/ QR code with printed name to identify your event attendee
If event management software is being used to set up a virtual meeting, passwords can be issued instead of tickets to allow delegates access to webinars and their corresponding documents.
Although it may seem unnecessary to implement such stringent security measures for smaller events, it is worth remembering that uninvited visitors can not only cause trouble but also reduce your return on investment, as exhibitors may shun away from future events if they always face gatecrashers at your events. If you can ensure only relevant delegates get in, you can increase your chances of your conference being a success and also increase customer delight at the same time.